This is for everybody’s reference, correction and updates.
Just read on, if there are improvements or a much better process in my way, feel free to comment and will integrate.

[itengrrandoms.design.blog] Daily I.T. stuff encountered, for everybody’s reference, correction and improvement.
This is for everybody’s reference, correction and updates.
Just read on, if there are improvements or a much better process in my way, feel free to comment and will integrate.

Now, we need to extend the partition in the server.
SSH to the EC2 instance where the EBS we’ve just extended is attached to.
Type the ‘lsblk’ command to list block devices:
A similar output should be shown:

As you can see size of the root volume reflects the new size, 50GB, the size of the partition reflects the original size, 16 GB, and must be extended before you can extend the file system.
# sudo growpart /dev/xvda 1

Next extend the file system.
Type “df -h” command to check extended file system.
A similar output should be shown:

As you can see size of the file system is still the original size of 16 GB, and must be resized.
# sudo resize2fs /dev/xvda1

You have just extended the EBS Volume in AWS of your Ubuntu Server with no downtime!

D-LINK Configuration | Screenshots


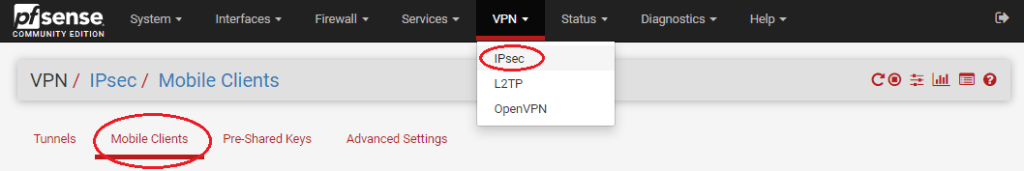
pfsense Configuration |
Certificate Authority (CA)






pfsense Configuration |
VPN / IPsec / Mobile Clients

pfsense Configuration |
VPN / IPsec / Tunnels




After VPN Configurations, VPN > Tunnels page will look like this:

pfsense Configuration |
Firewall > Rules

Remote User Configuration |
Windows 10
Download first the crt file from pfsense and send to the remote user.
This cert file will be needed to be Installed in the user’s terminal.

* After distributing the crt file from pfsense to the remote users, share the instructions below regarding the installation of the certificate and the creation of VPN connection.
 by the CA to download only the certificate
by the CA to download only the certificate
Downloaded CA Certificate

Certificate Properties

Certificate Import Wizard – Store Location

Certificate Import Wizard – Browse for the Store

Select Certificate Store

Completing the Certificate Import Wizard
Setup VPN Connection in Windows 10 Remote User


Setup VPN Connection in an Android Remote User






To check for your existing nginx logs, go to :
# cd /var/log/nginx


Move all logs to /backup/anyname.com/log

#cd /etc/logrotate.d
sudo nano /etc/logrotate.d/anyname.com
1 /var/log/nginx/anyname.com/*access_log
2 /var/log/nginx/anyname.com/*error_log
3 {
4 daily
5 missingok
6 rotate 10
7 dateext
8 compress
9 delaycompress
10 create 644 dev root
11 sharedscripts
12 lastaction
13 cp /var/log/nginx/anyname.com/*.gz /backup/anyname.com/log
14 rm /var/log/nginx/anyname.com/*.gz
15 systemctl restart nginx
16 endscript
17 }

1 #!/bin/sh
2
3 # Clean non existent log file entries from status file
4 cd /var/lib/logrotate
5 test -e status || touch status
6 head -1 status > status.clean
7 sed 's/"//g' status | while read logfile date
8 do
9 [ -e "$logfile" ] && echo "\"$logfile\" $date"
10 done >> status.clean
11 mv status.clean status
12
13 test -x /usr/sbin/logrotate || exit 0
14 /usr/sbin/logrotate /etc/logrotate.conf
DONE!
Logrotation will be done daily.
Then after, will be moved to /backup

Go to : https://dash.cloudflare.com/login then Sign up.

Make sure to use a valid email address and follow the password requirements.

Cloudflare will ask right away for a site that can be added.
My site domain is called “itengrexamplesite.com” so I will add this site.

